akash@nvidia:~$ whoami --verbose
## IDENTITY ─────────────────────────────────────────
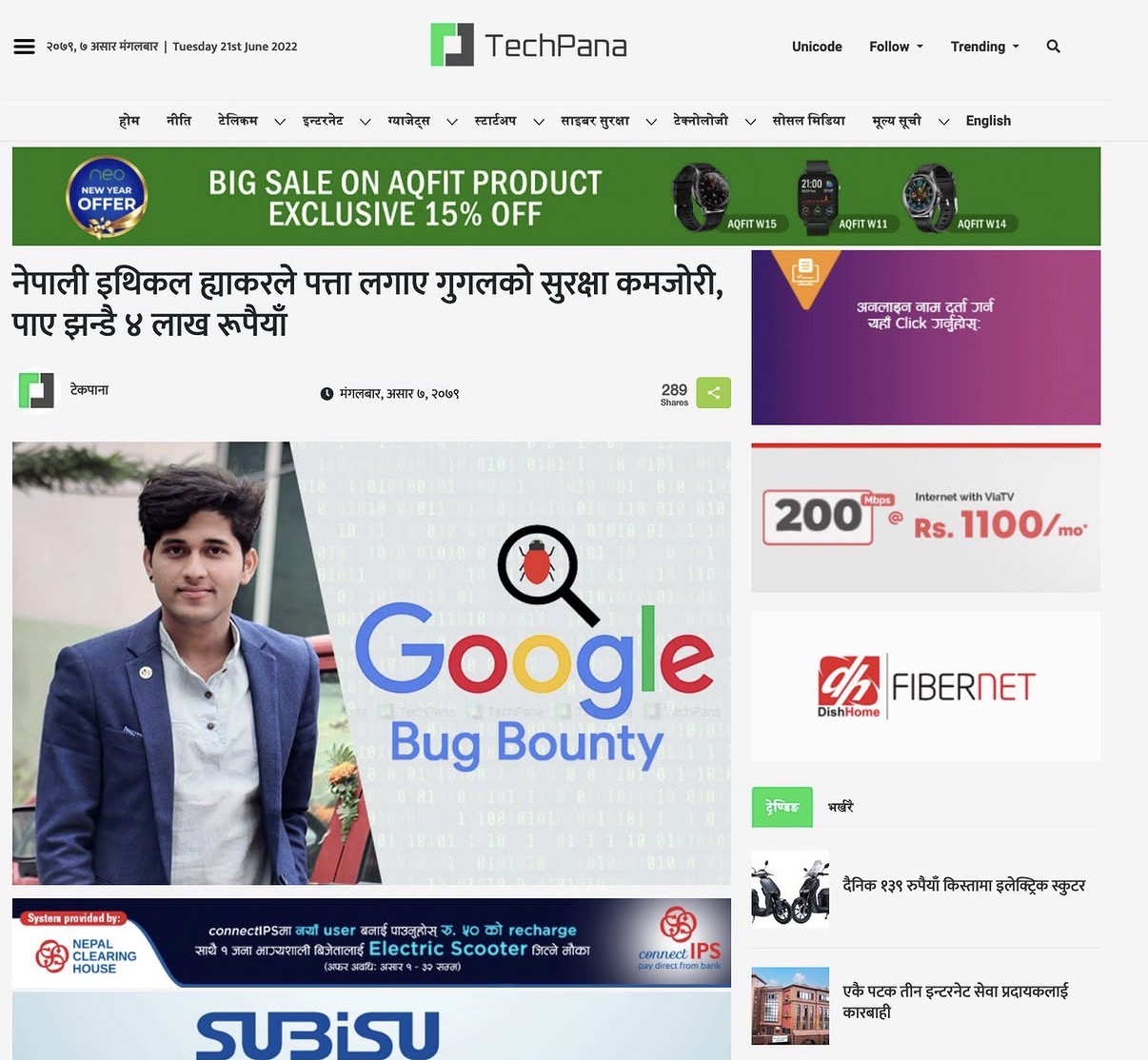
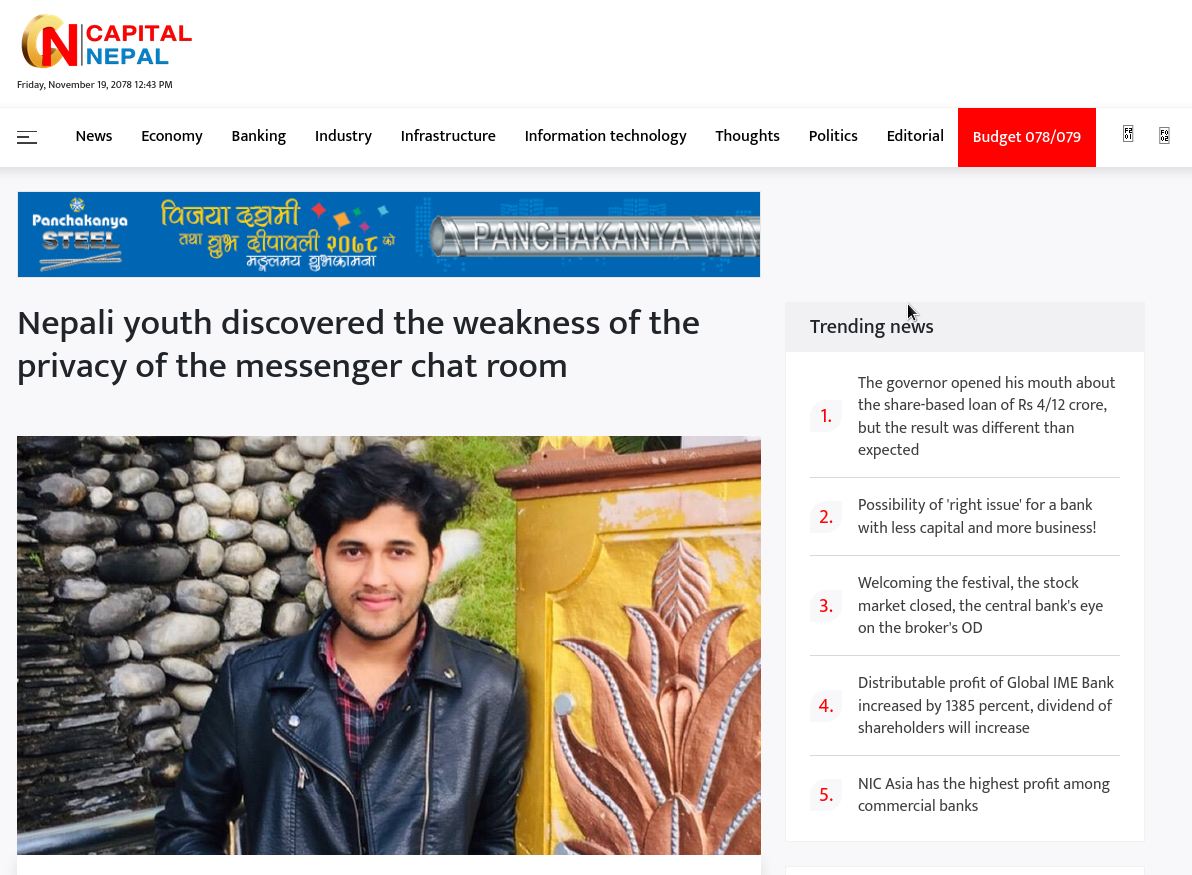
name » Akash Basnet
alias » @Noneofyou
base » Sunnyvale, CA, USA 🇺🇸
origin » Jhapa, Nepal 🇳🇵 (countryside)
email » basnetakash46@gmail.com
## EXPERIENCE ───────────────────────────────────────
cybsec » 2+ yrs · hands-on security researcher
it » 8+ yrs · IT specialist
## CURRENT ──────────────────────────────────────────
work » NVIDIA — Technical Support Analyst (SRO)
since » Jan 2026
scope » global endpoint support · Win/macOS/Linux
## BUG BOUNTY HALL OF FAME ──────────────────────────
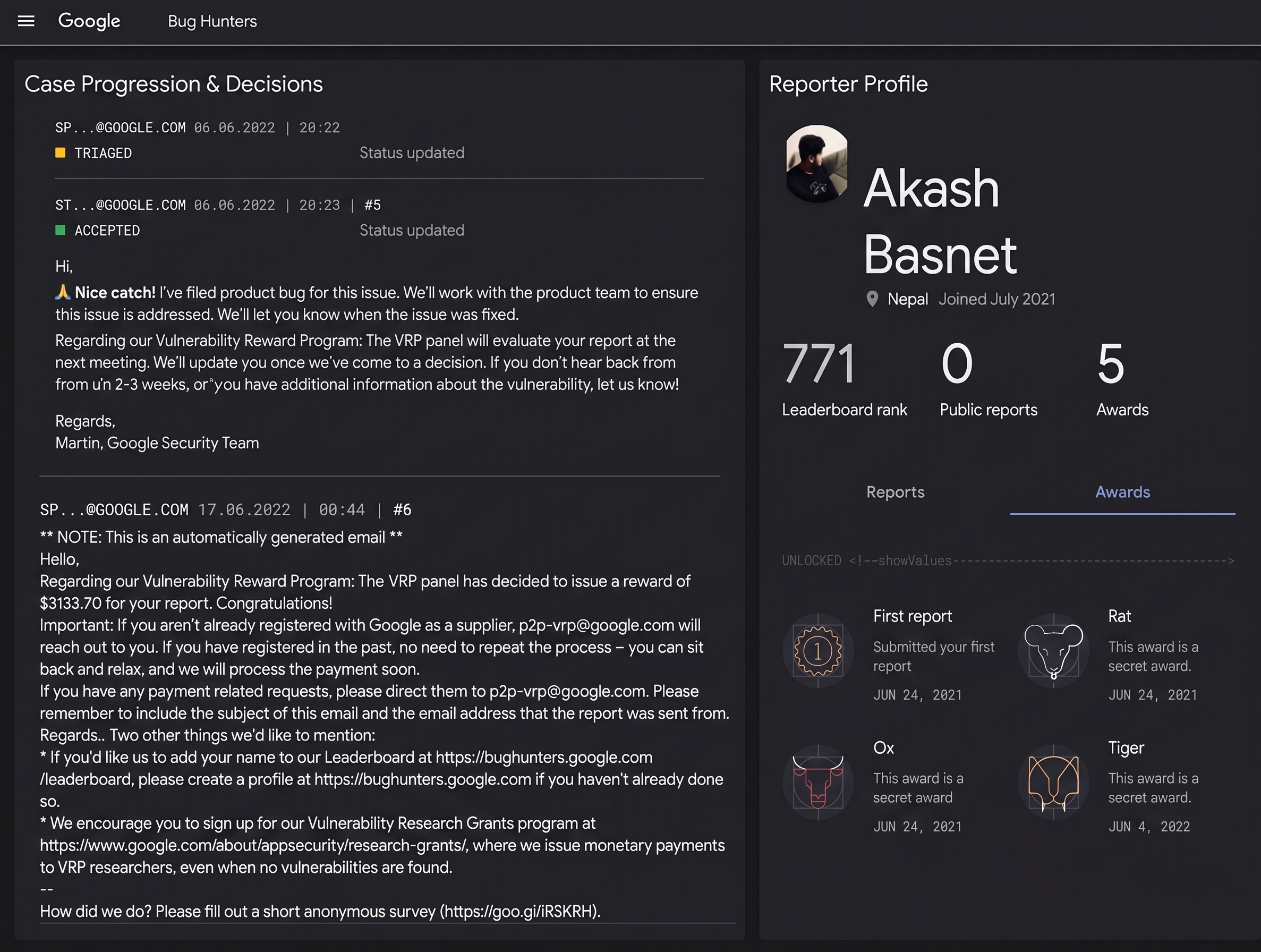
google » $10K+ · "Nice catch" — Google Security Team 🎯
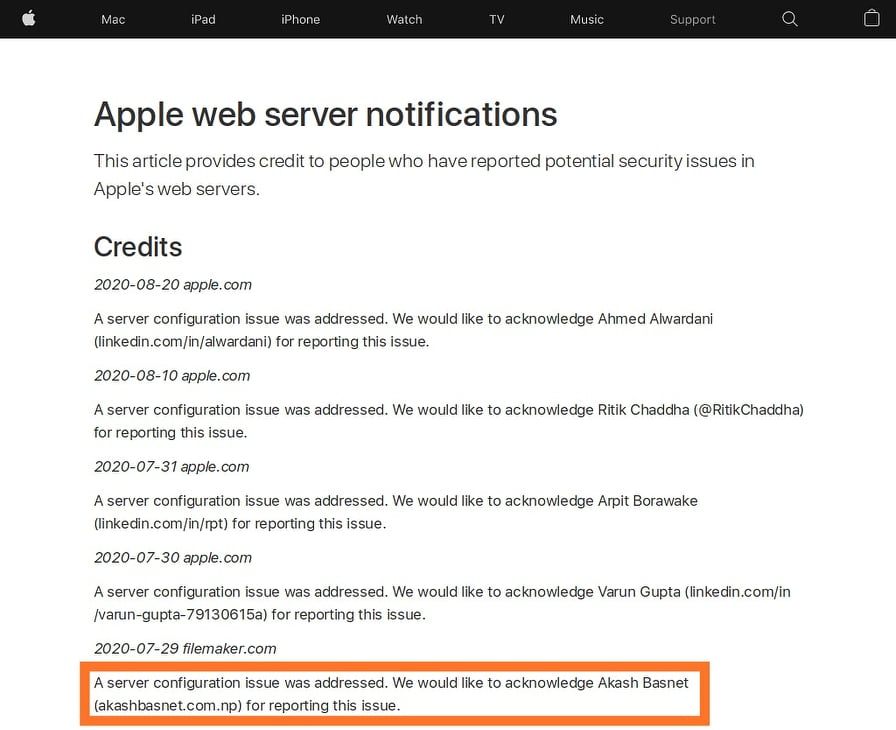
apple » apple.com Security Acknowledgements 2020
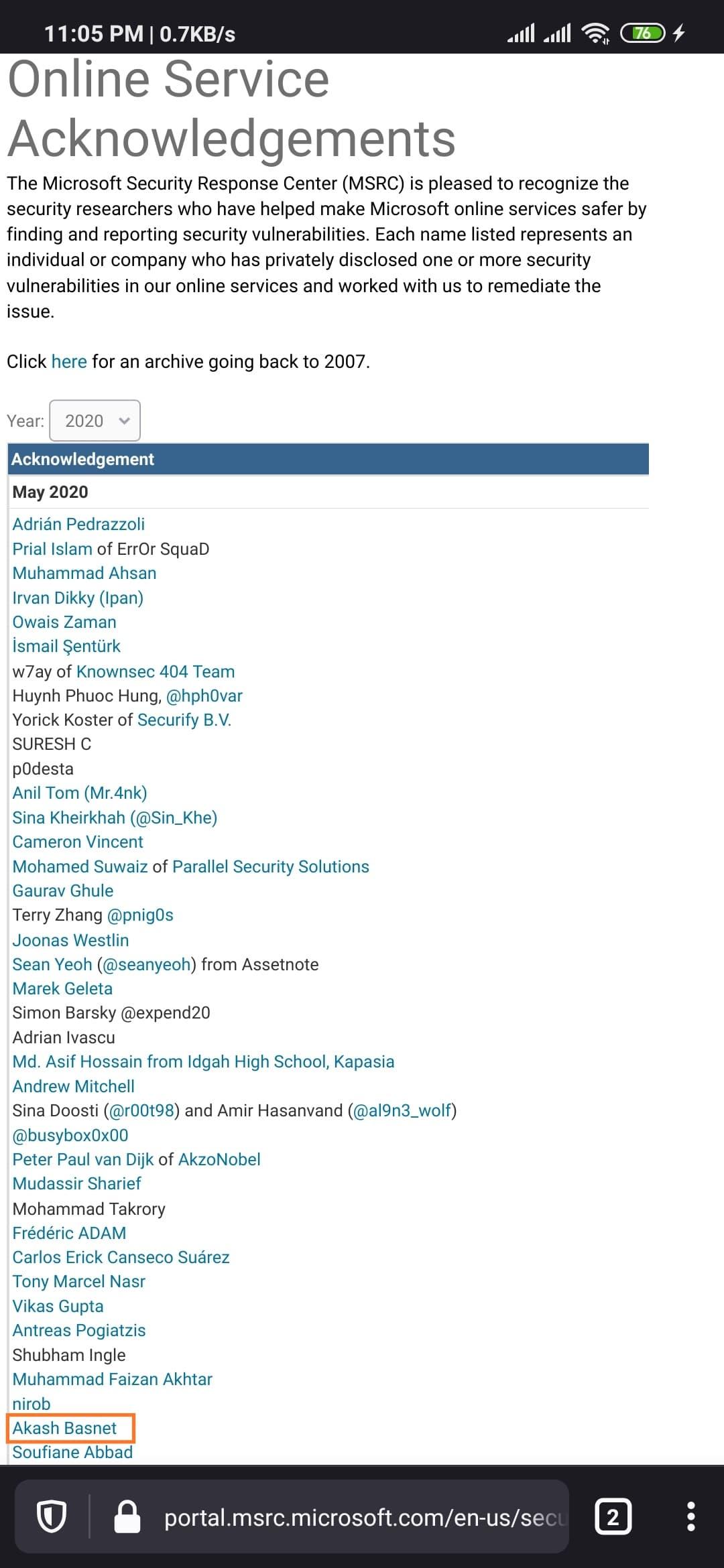
msft » MSRC Acknowledgements 2020
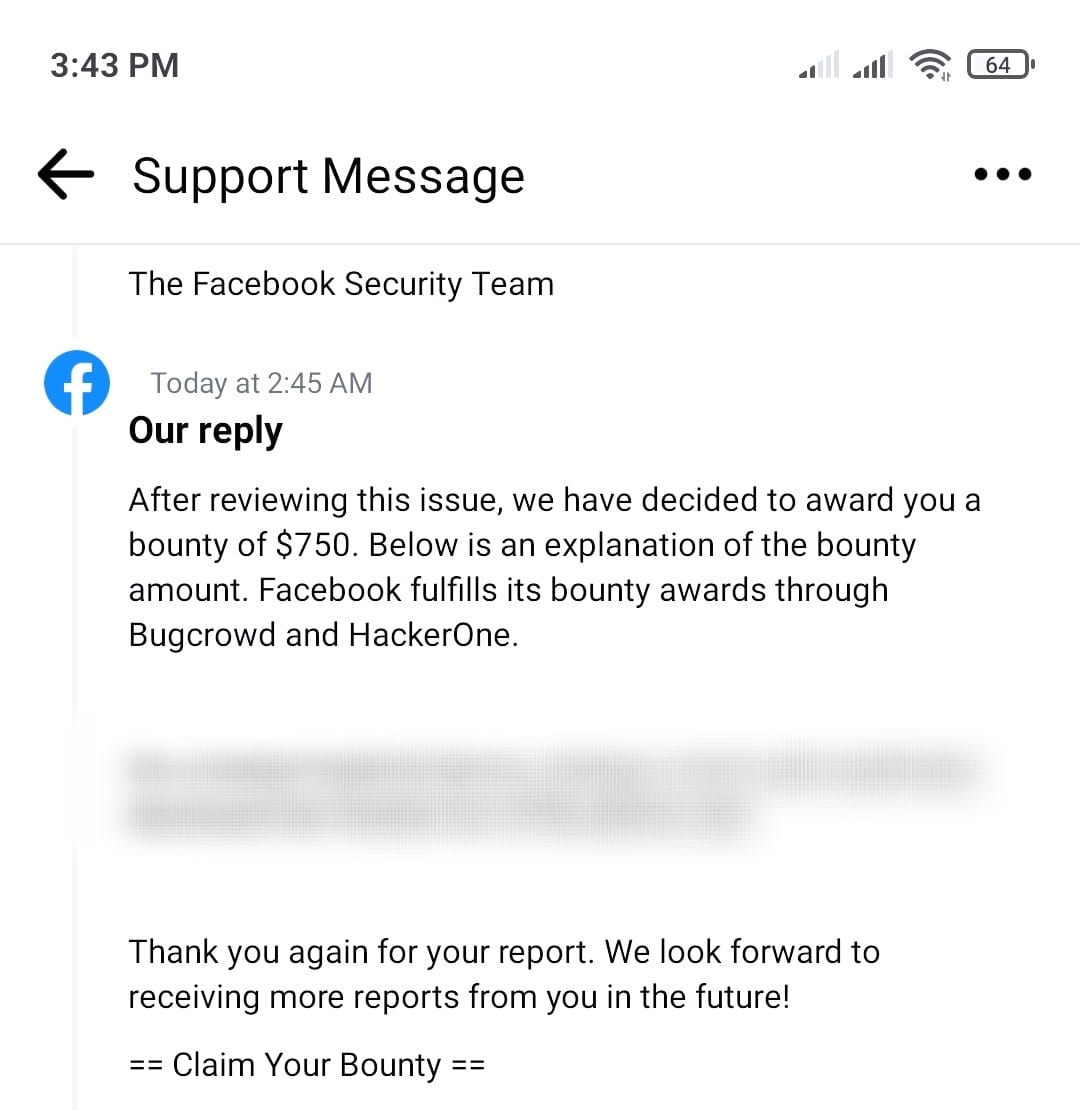
meta » facebook.com/whitehat — Hall of Fame
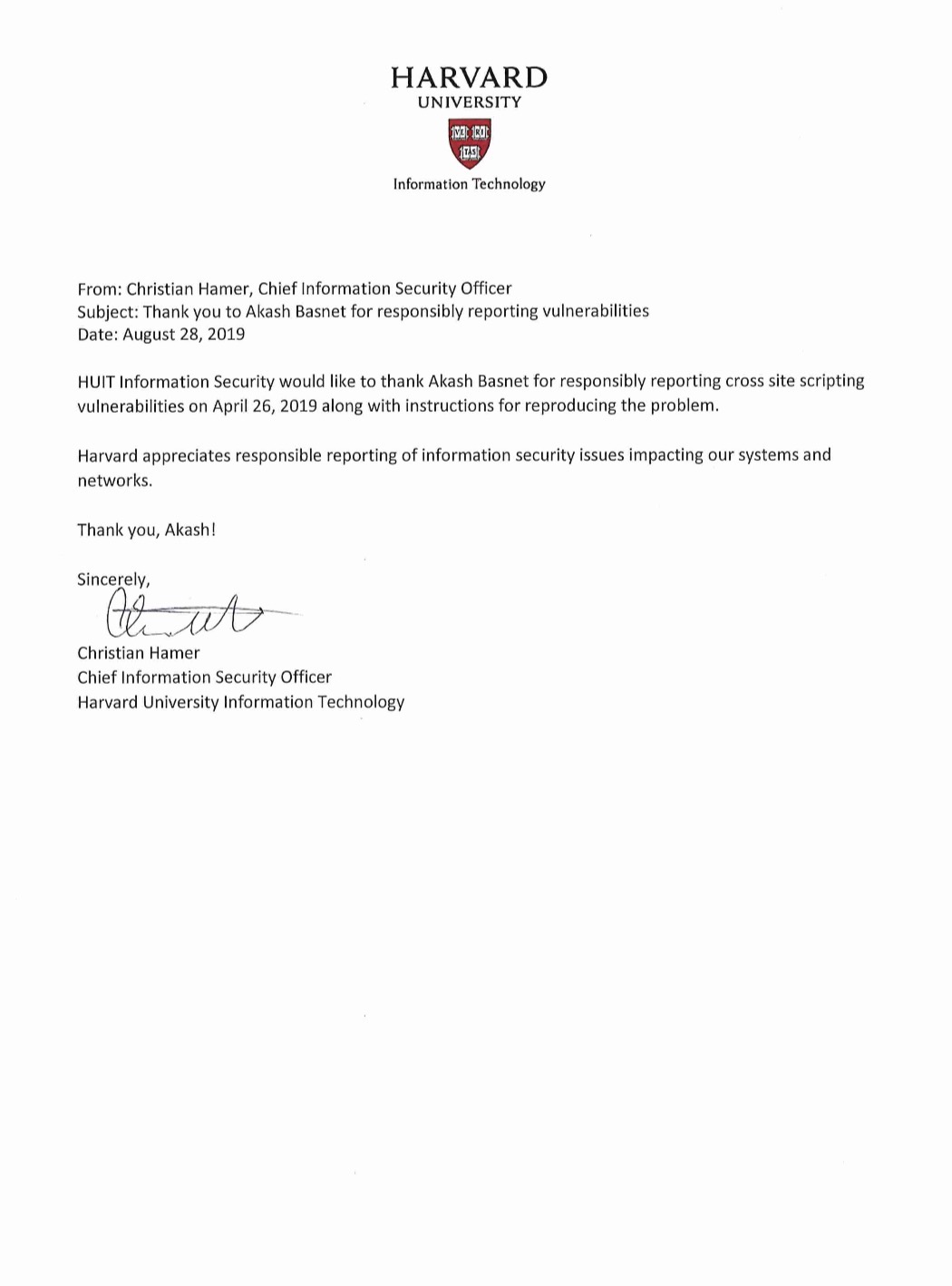
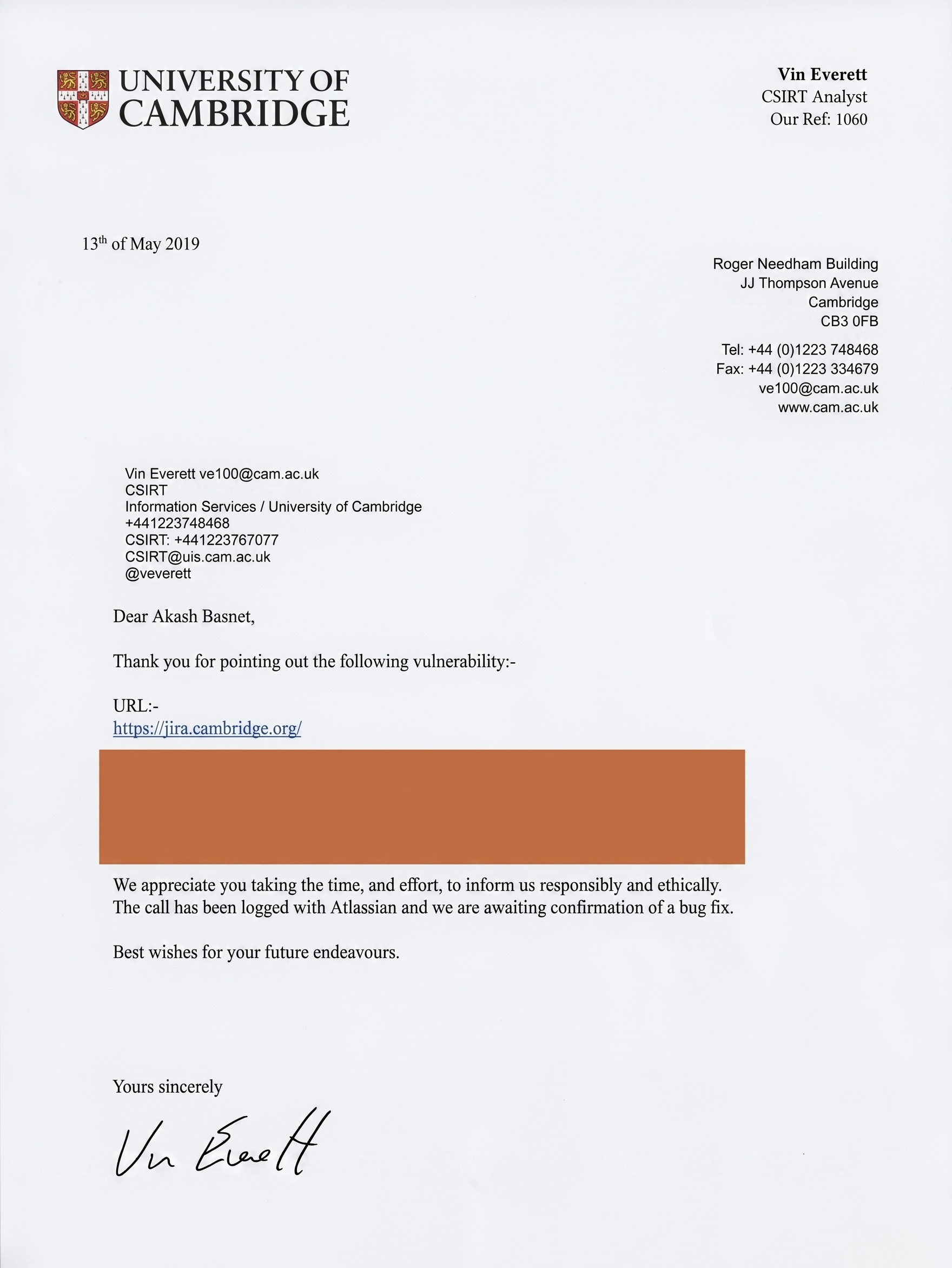
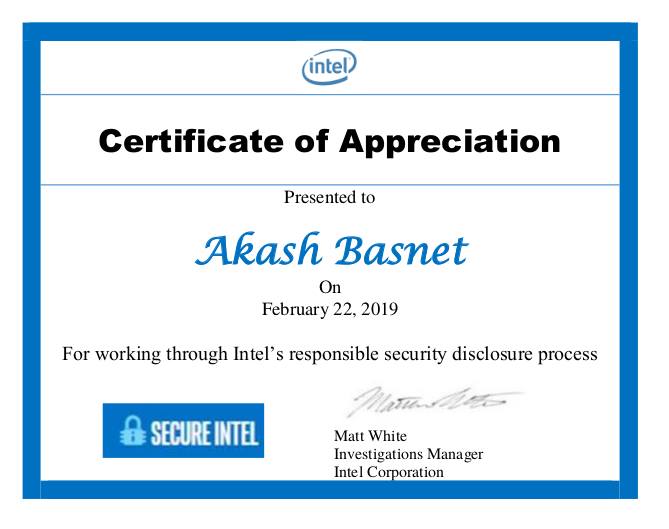
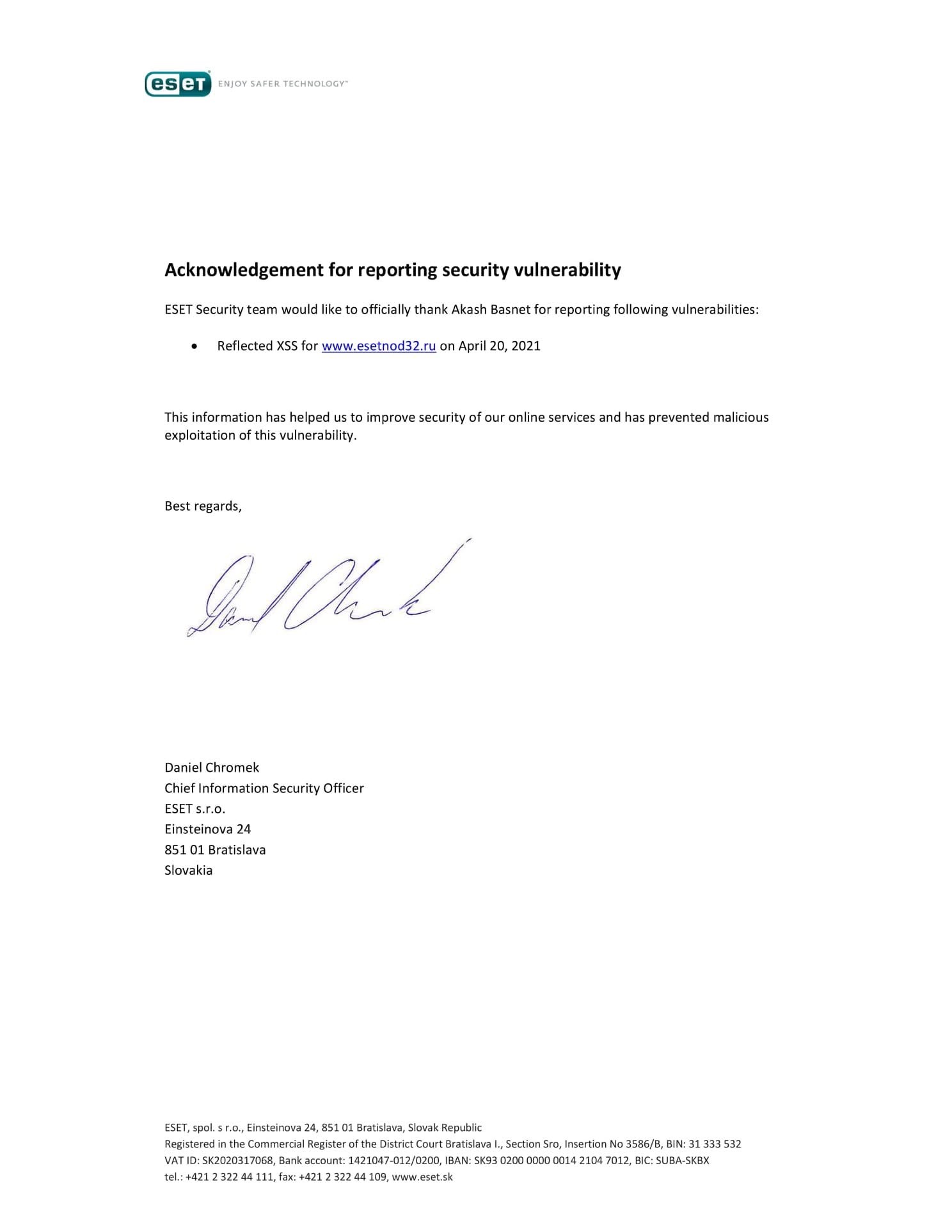
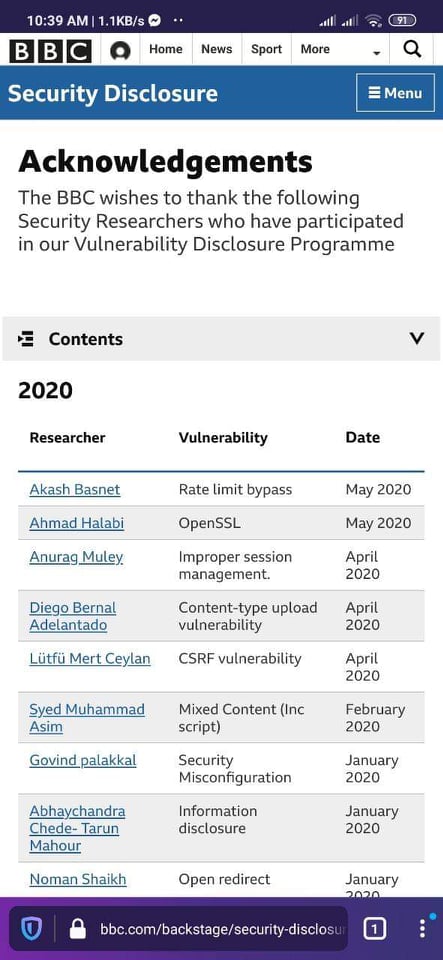
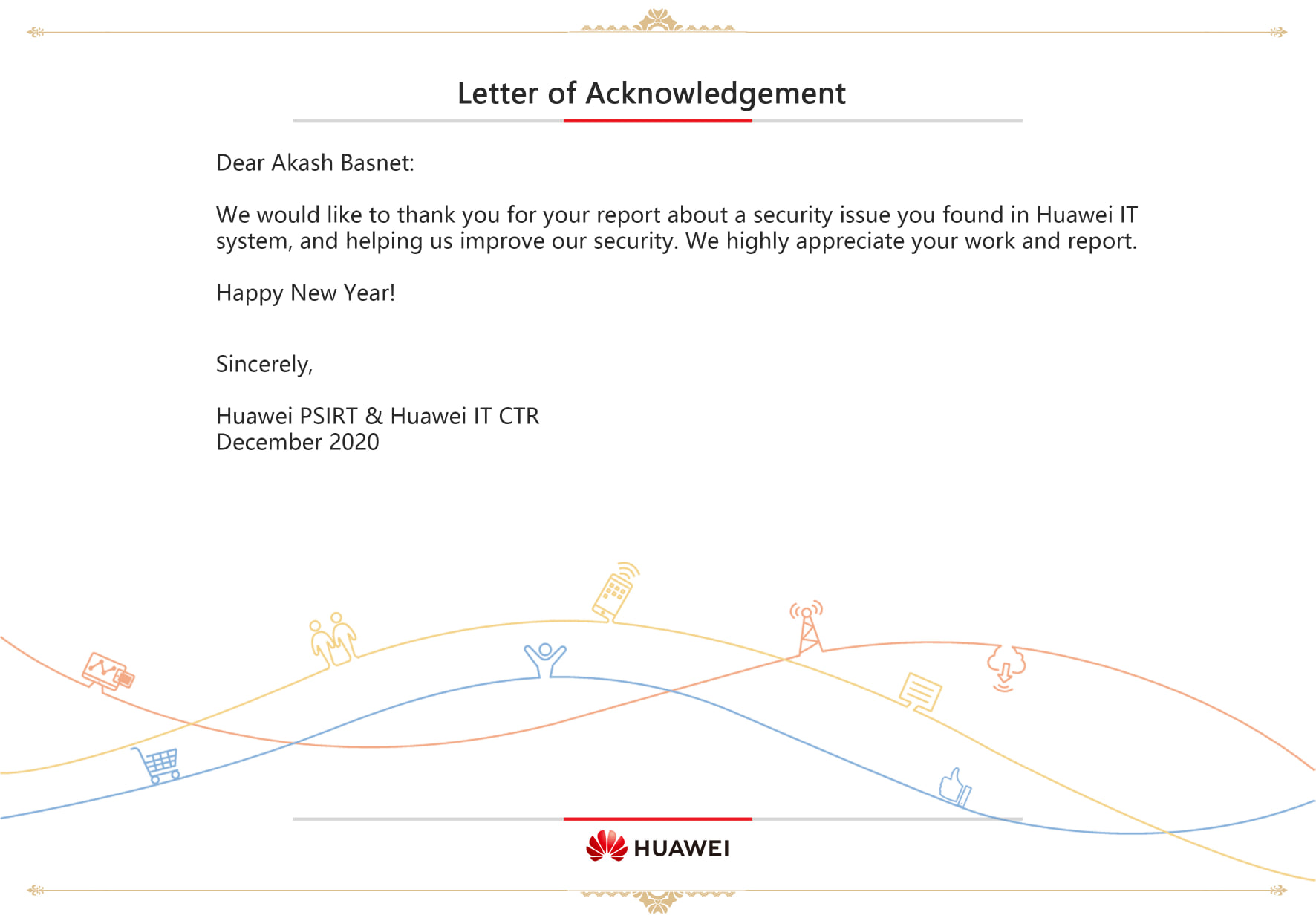
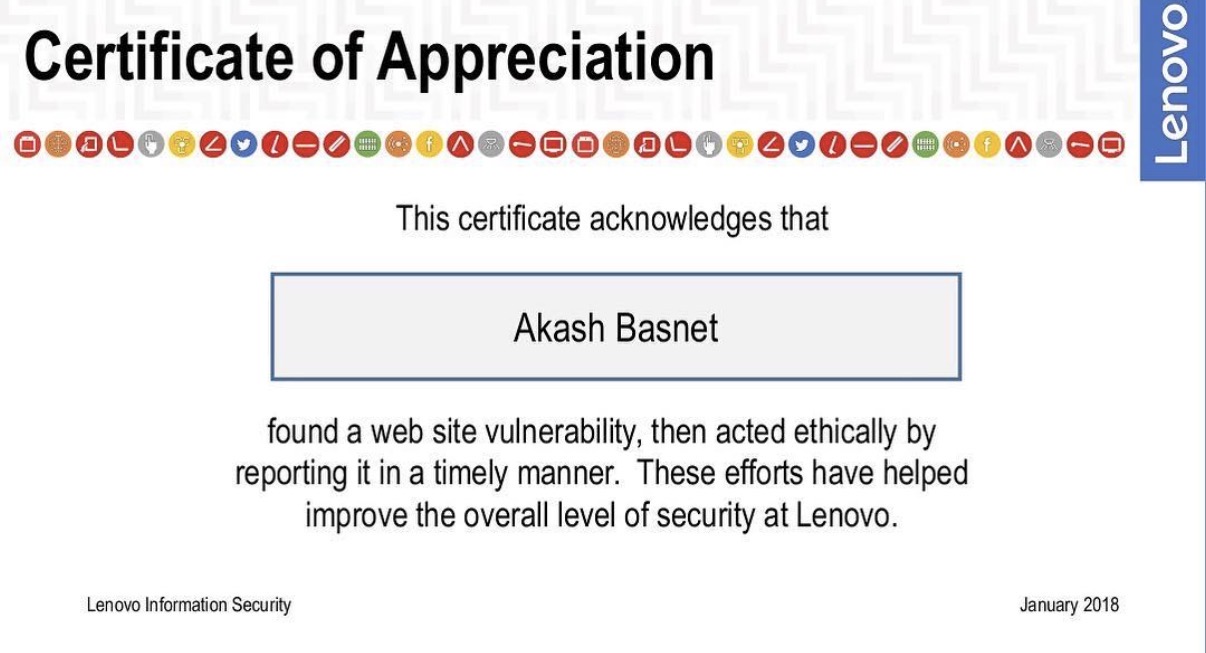
+ » BBC News, Harvard, Cambridge, ESET, McAfee,
Intel, Lenovo, Huawei, Nokia, Hamropatro, Kantipur
## CTF & CONFERENCES ────────────────────────────────
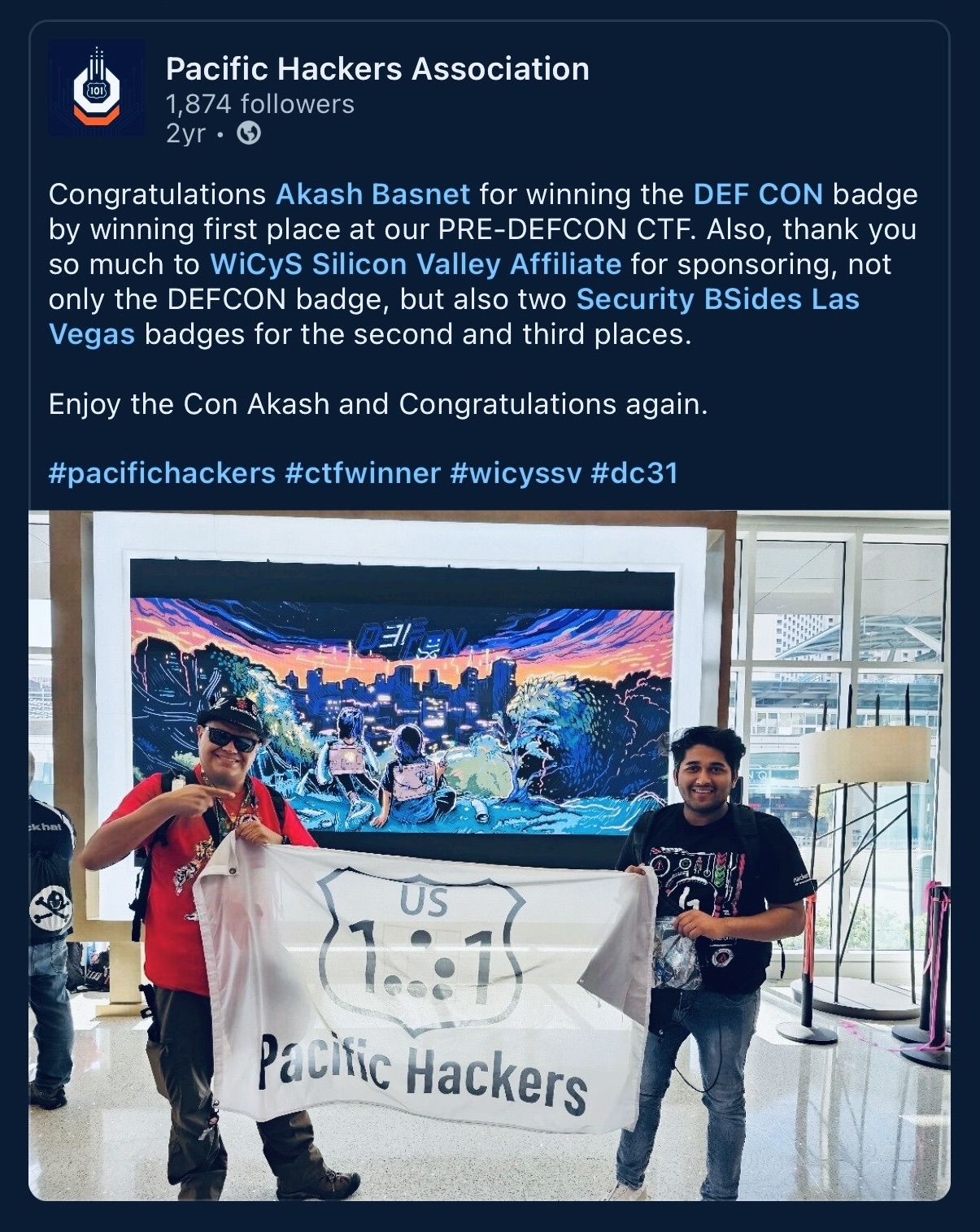
winner» 🥇 Pre-DEF CON CTF — HackerDojo, Silicon Valley
defcon» attended × 2 · Caesars Palace, Las Vegas
blkhat» Black Hat USA · attended × 1, Las Vegas
wiz » Wiz CTF — Top 50 / 500
dod » DoD USA CTF — Top 500 / 5,000
## NEPAL FEDERAL GOV ────────────────────────────────
secured» Singha Durbar · PMO · 5 ministries
─────────────────────────────────────────────────────
akash@nvidia:~$ still hunting